Patterns of CNA behavior for April 2026 worth noting
A publicly exploitable Linux kernel vulnerability dubbed 'Copy Fail' allows any unprivileged local user to silently overwrite root-owned binaries and seize full system control. Kernels from version 4.14 through 6.18.21 are affected, and a working Python exploit is already public.
A trivially exploited authentication bypass in ConnectWise ScreenConnect — requiring nothing more than appending a slash to a URL — hands attackers SYSTEM-level control over entire managed IT networks, and ransomware crews are already cashing in.

A perfect CVSS 10.0 vulnerability in Atlassian Confluence lets anyone on the internet create an admin account with a single HTTP request. Nation-state actors and ransomware gangs are already exploiting it.

Cisco discloses CVE-2026-20131, a maximum-severity unauthenticated remote code execution vulnerability in its Secure Firewall Management Center. Attackers can gain root access by sending a single crafted request — no credentials required.

A perfect-10 authentication bypass in Cisco's SD-WAN Controller and Manager lets unauthenticated attackers seize control of enterprise wide-area networks. Cisco confirms active exploitation, CISA issues Emergency Directive 26-03.

A 2022 privilege escalation vulnerability in Cisco SD-WAN software is now being actively exploited in the wild, four years after patches were released. Attackers with any valid local credential can chain two path traversal bugs to seize complete root control of routers, controllers, and orchestra...

A critical OS command injection vulnerability in Soliton's FileZen file-sharing appliance is being actively exploited in the wild, giving attackers full remote code execution. A patch has been available since January — but many systems remain exposed.
A perfect CVSS 10.0 vulnerability in Dell RecoverPoint for Virtual Machines ships with hard-coded Tomcat credentials that a Chinese-linked threat group has been exploiting since mid-2024 to deploy backdoors and ransomware.

CISA added CVE-2008-0015 to its Known Exploited Vulnerabilities catalog on February 17, 2026, confirming active exploitation of a critical stack-based buffer overflow in Microsoft's Video ActiveX control that allows complete system takeover via a malicious webpage.
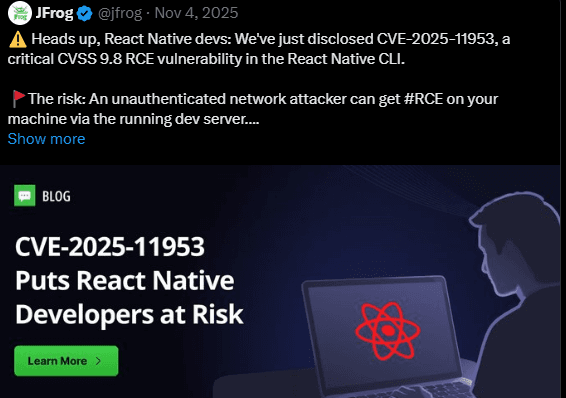
A trivially exploitable command-injection vulnerability in the React Native CLI's Metro development server is being actively exploited in the wild. CISA has added CVE-2025-11953 to its Known Exploited Vulnerabilities catalog — here's what every React Native team needs to know right now.
.png&w=3840&q=75)
A critical authentication bypass in OpenSSH (CVE-2025-26465) has lurked undetected since 2014, allowing attackers to impersonate any SSH server when a rarely-enabled option is configured. The vulnerability affects all releases from 6.8p1 through 9.9p1.

Microsoft patched CVE-2026-20805, a Desktop Window Manager information disclosure flaw actively exploited to defeat memory protections. CISA added it to the KEV catalog, requiring federal agencies to patch by February 3, 2026.

A critical vulnerability dubbed 'MongoBleed' allows unauthenticated attackers to extract sensitive data from MongoDB server memory through malformed Zlib headers. CISA confirms active exploitation in the wild.

A critical command injection flaw in DigiEver surveillance devices is being actively exploited by multiple botnets. The vendor has refused to patch, leaving thousands of devices permanently vulnerable.

A maximum-severity (CVSS 10.0) vulnerability in React Server Components is being actively exploited by Chinese state-sponsored actors and ransomware groups. The flaw allows unauthenticated remote code execution on servers running default configurations of Next.js and other React frameworks.

A critical authentication bypass in Kentico Xperience CMS lets attackers log in with only a username, chain to file-write, and execute code. Fixed in 13.0.178; CISA confirms active exploitation since Dec 2024.